FILE HASH GENERATION GUIDE DISCLAIMER Under no circumstances shall the Department of Justice be liable for any losses and/or dam

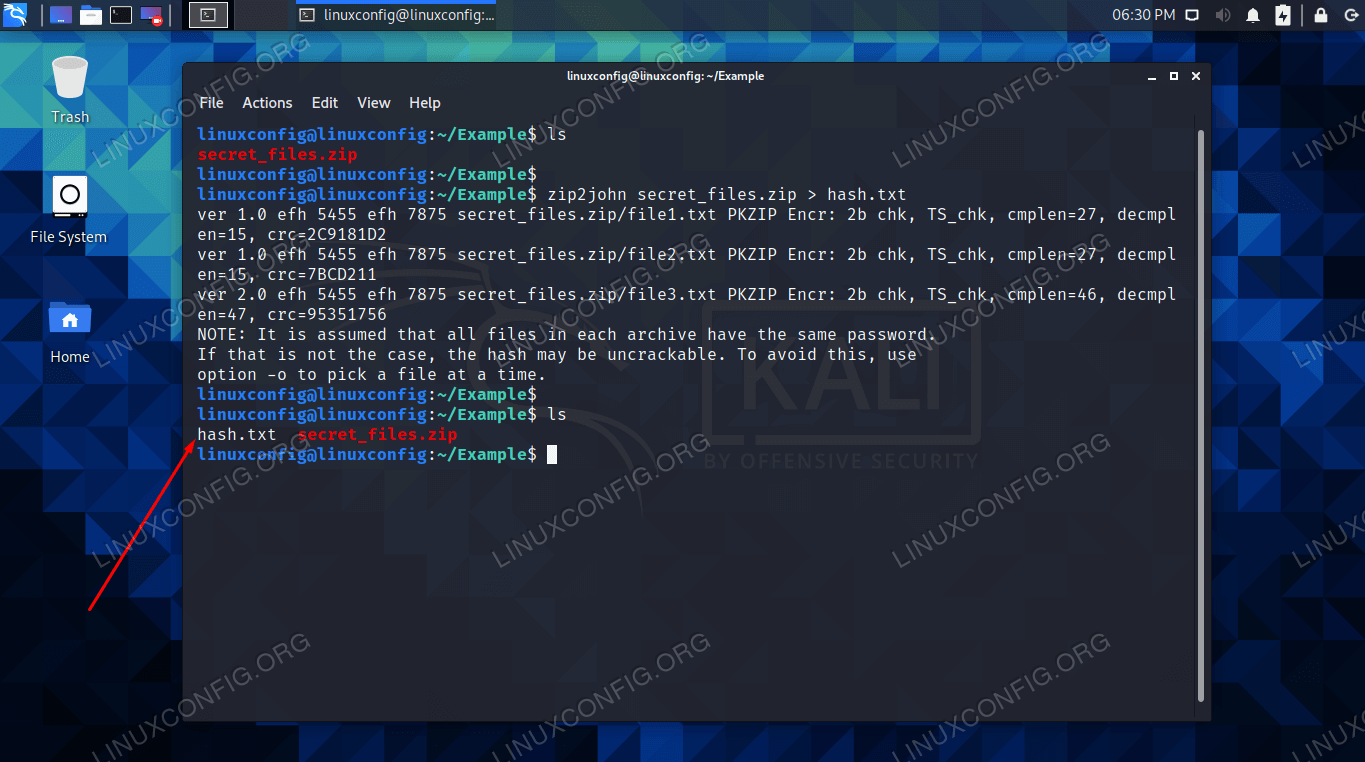
Comprehensive Guide to John the Ripper. Part 4: Practical examples of John the Ripper usage - Ethical hacking and penetration testing
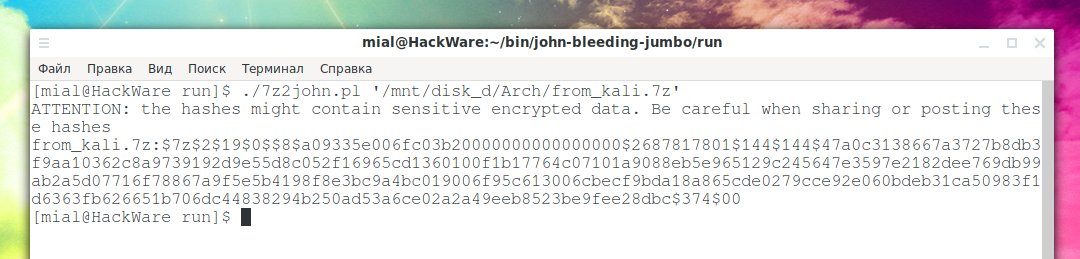
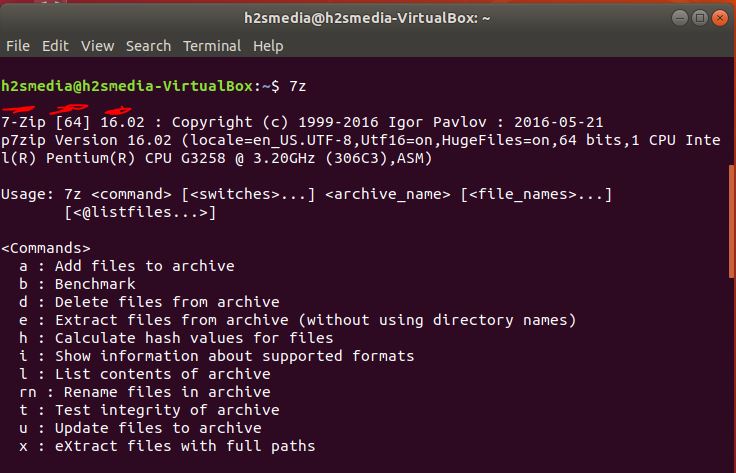
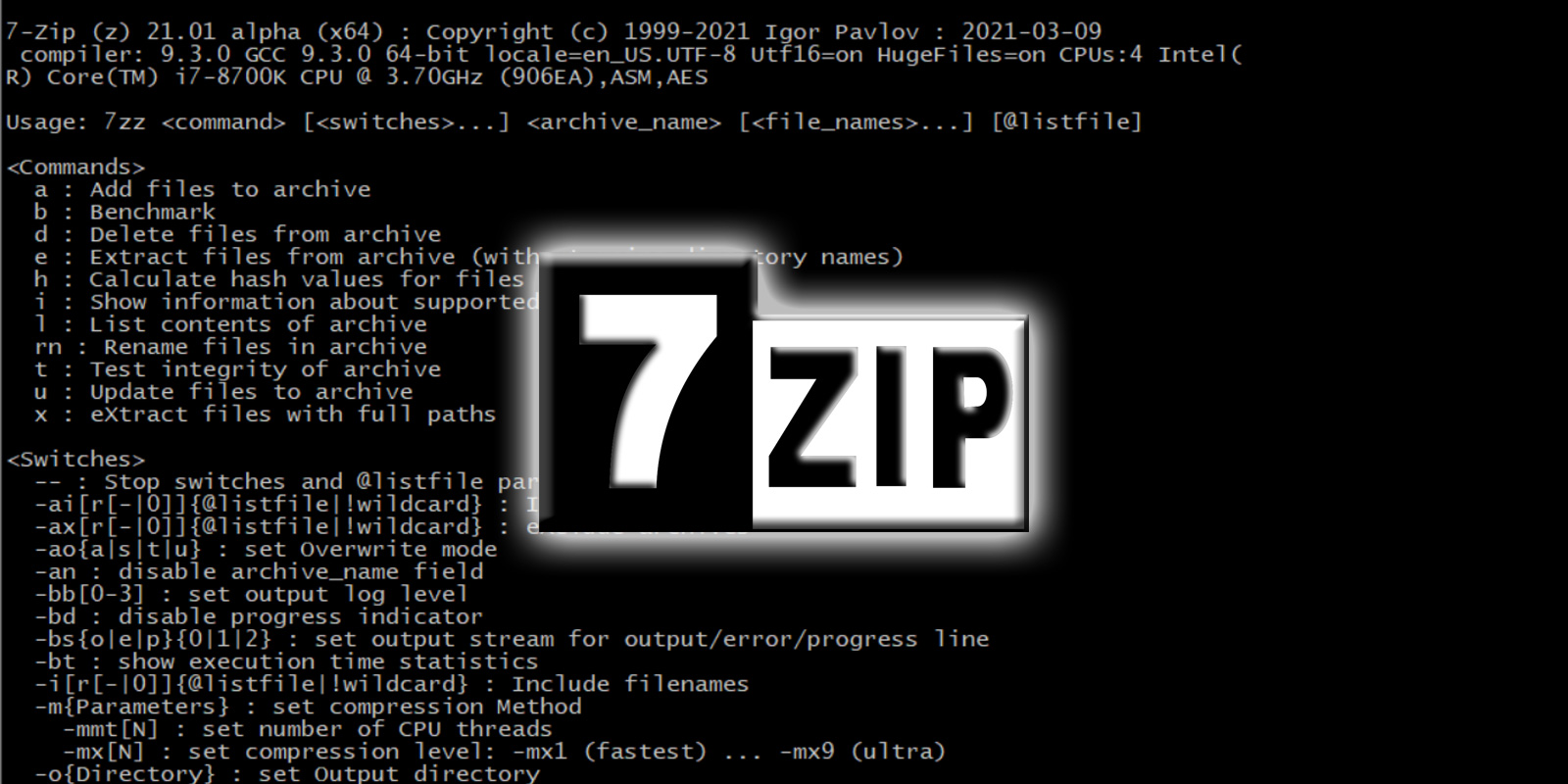
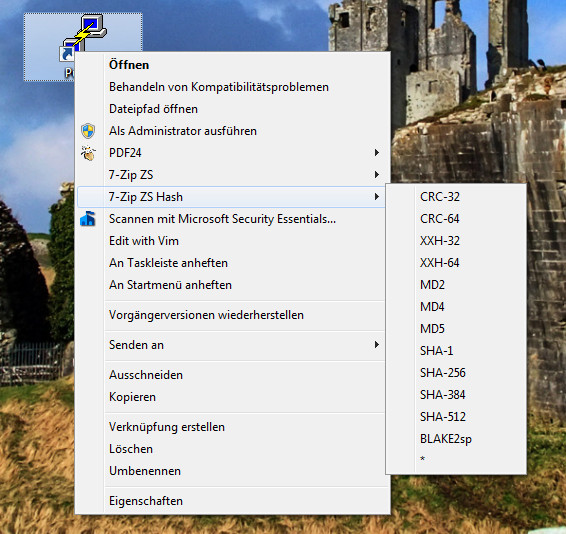
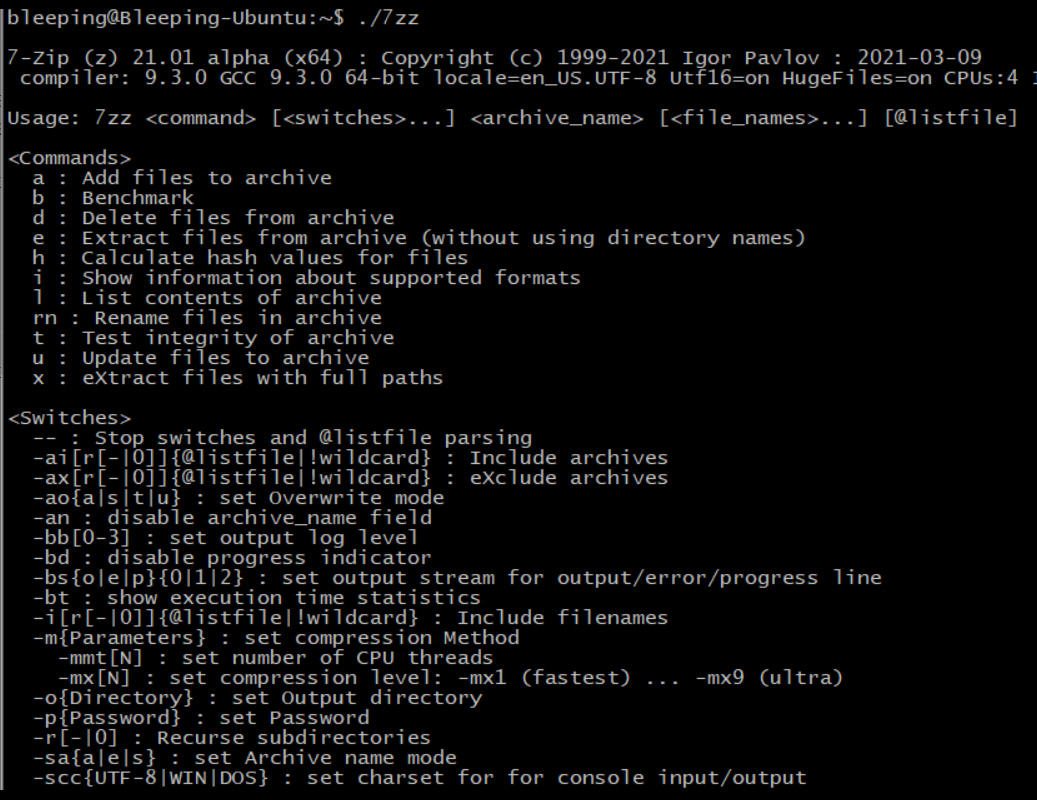
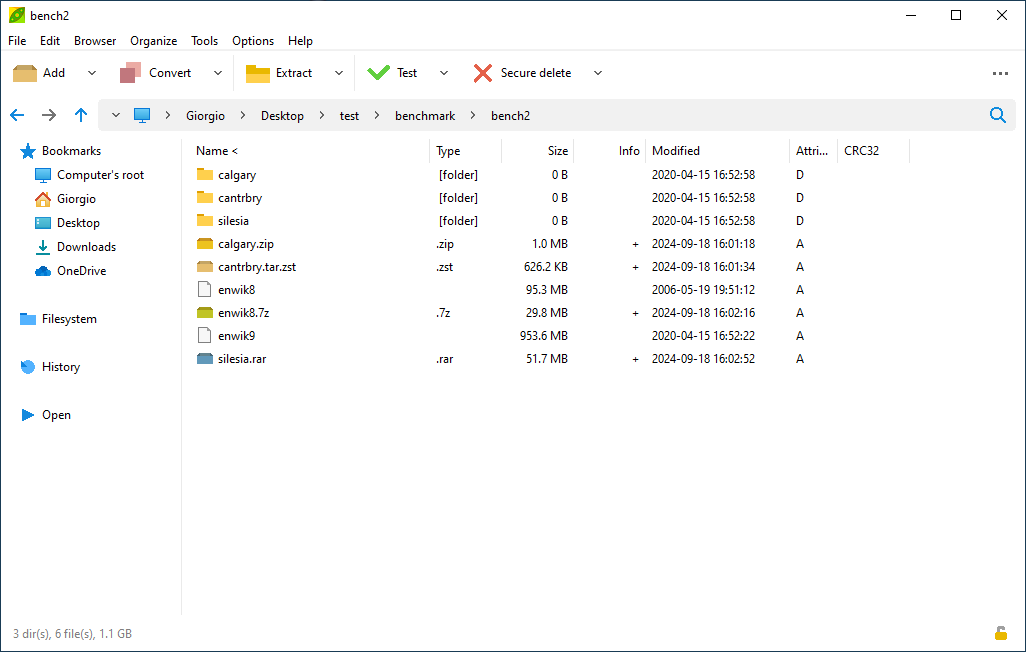
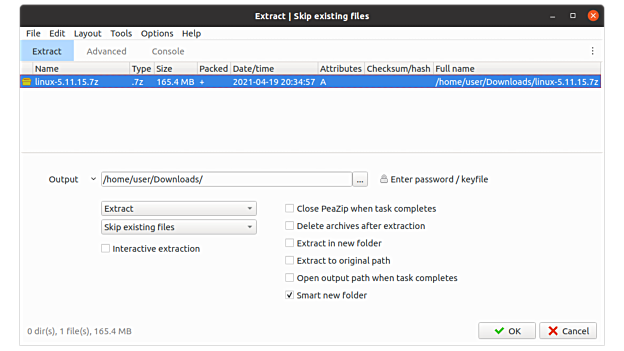
Comprehensive Guide to John the Ripper. Part 2: Utilities for extracting hashes - Ethical hacking and penetration testing