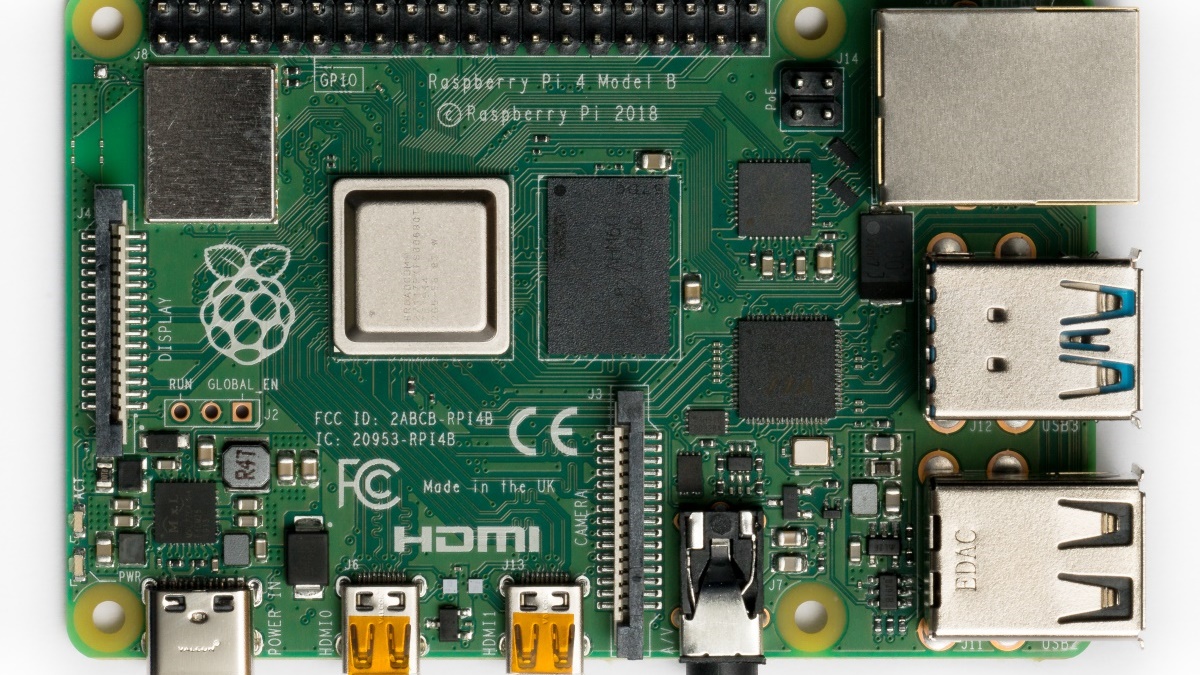
Security on a Budget: Turning a Raspberry Pi 4 into a Low-Budget, Zeek based Network Monitoring Sensor – Dan Gunter

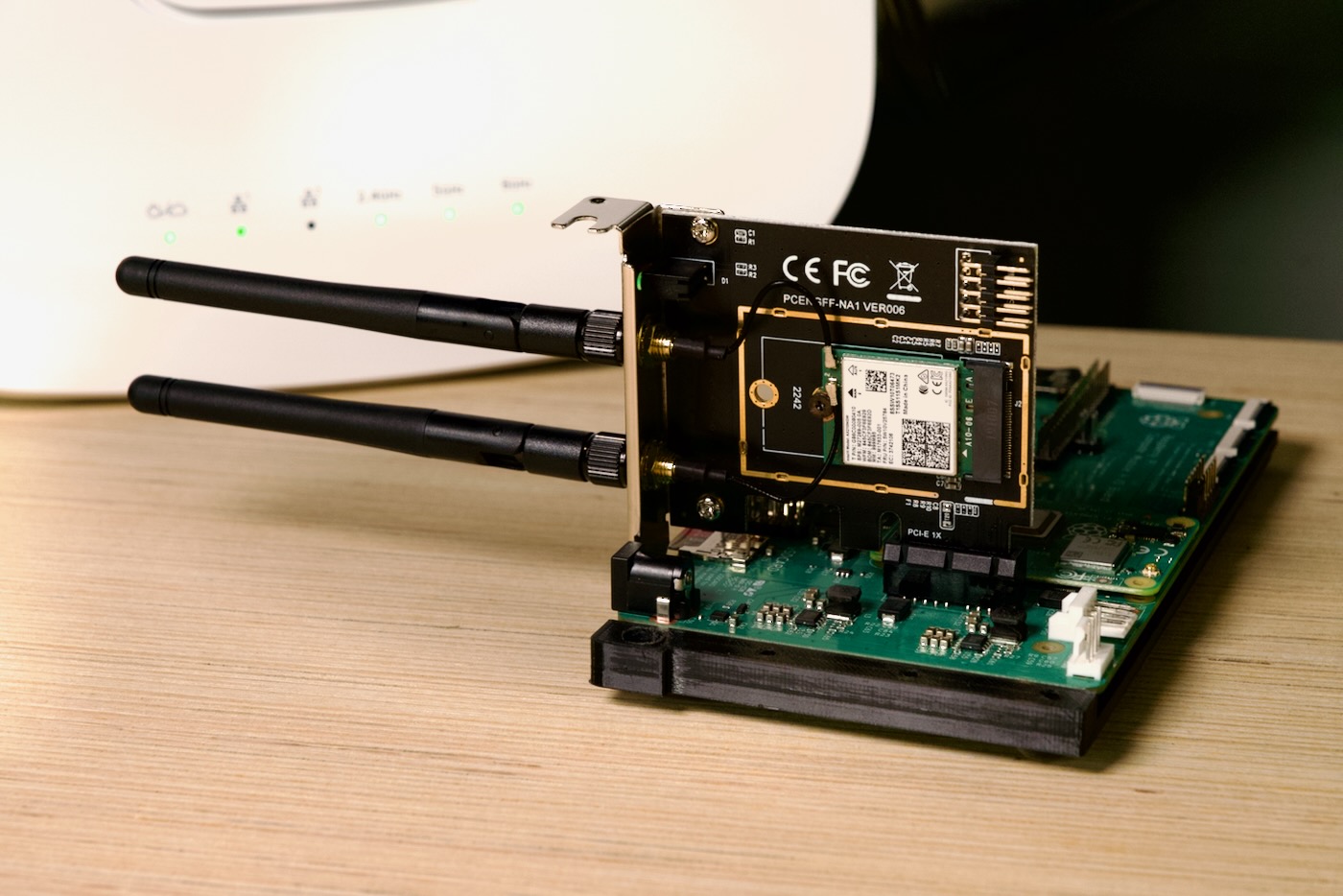
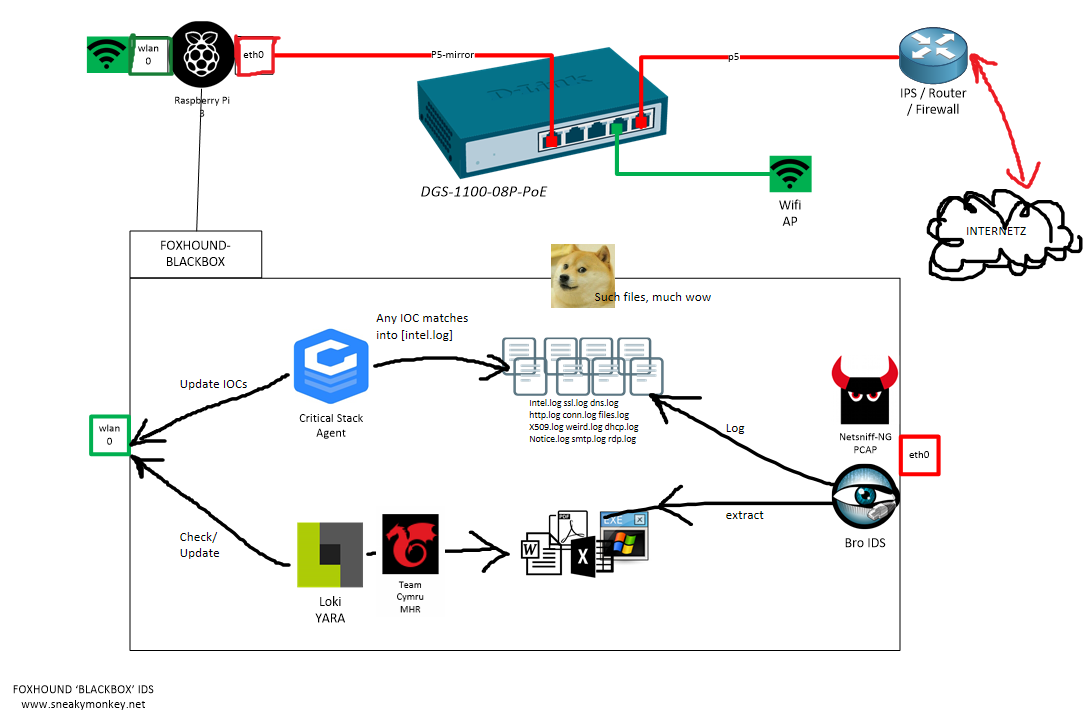
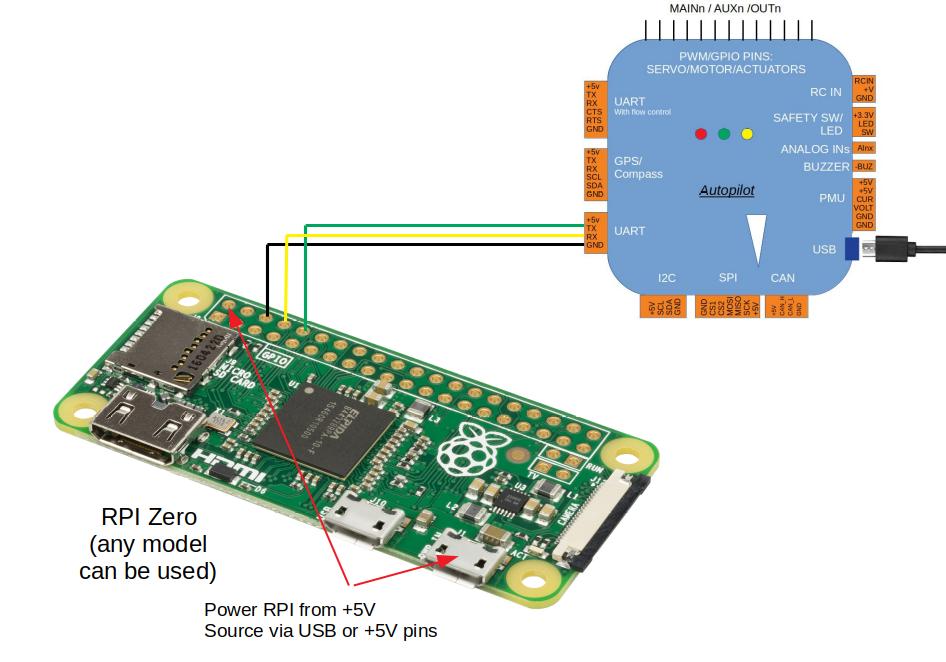
Experimental Setup showing (a) Raspberry Pi, and (b) IDS configurations... | Download Scientific Diagram

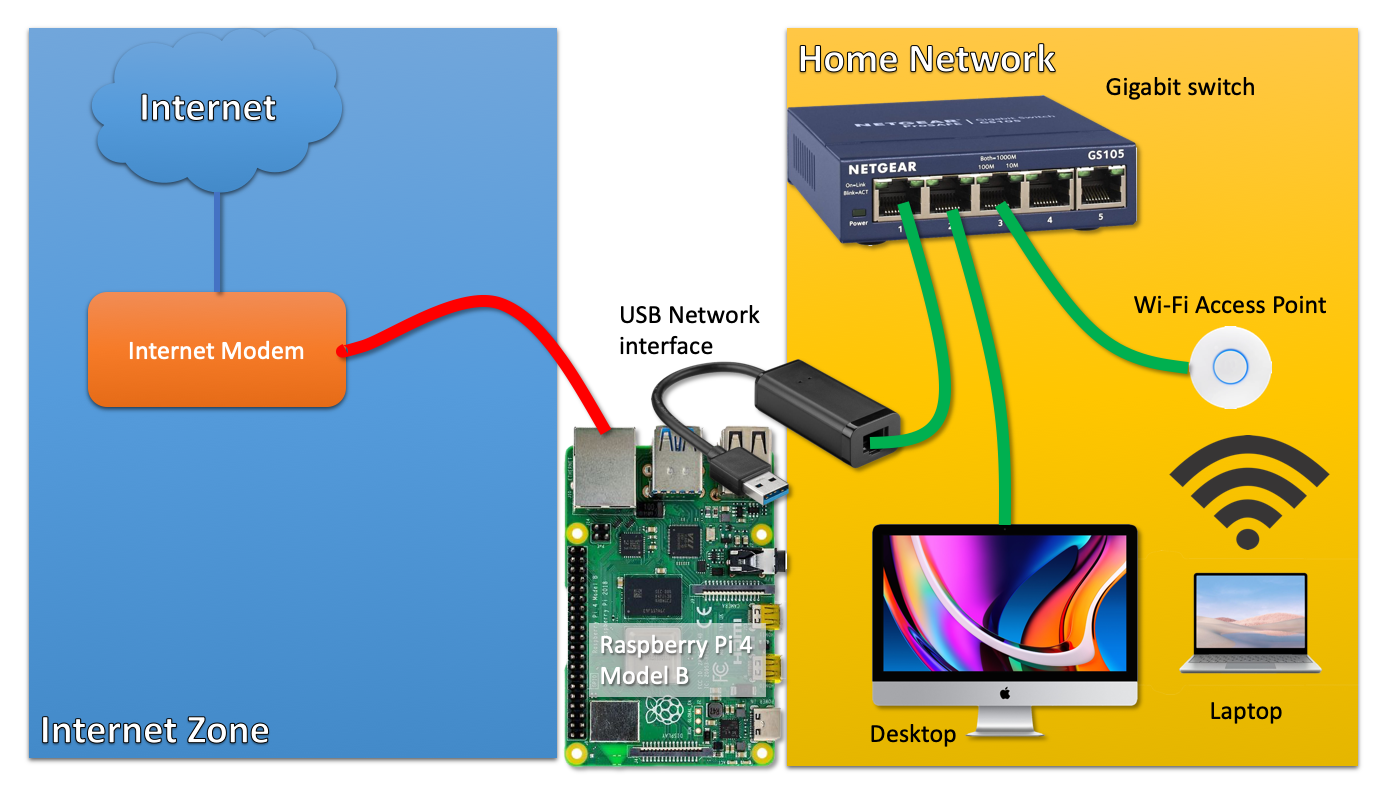
Spot suspicious activity on your local network with Suricata Intrusion Detection System (IDS) on Raspberry Pi – Juliana Fajardini
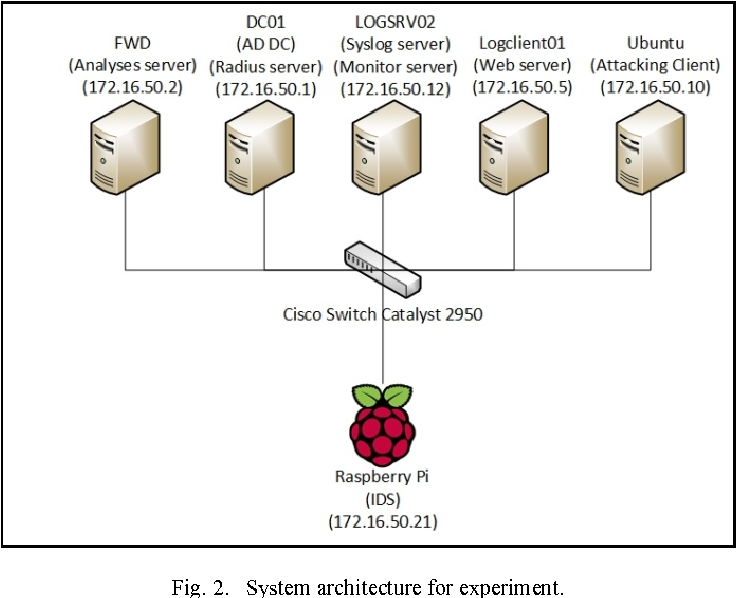
Figure 2 from Pi-IDS: evaluation of open-source intrusion detection systems on Raspberry Pi 2 | Semantic Scholar

Figure 4 from Intrusion Detection System Using Raspberry PI Honeypot in Network Security | Semantic Scholar

Figure 3 from The security of RFID readers with IDS/IPS solution using Raspberry Pi | Semantic Scholar